E-mail Analysis - Tips & Resources
Tips and resources on how to have a better understanding of phishing attacks using e-mail messages.

Summary
At the present moment, phishing is still considered one of the most frequent ocurrencies of fraudulent activity on the Internet.
More often than not, an email message containing a link or an attachment can lead to severe losses for their aimed victims including the data breach of sensitive information and identity theft.
According to IBM’s 2022 Cost of a Data Breach Report, “In 2022, the most common initial attack vectors were compromised credentials at 19% of breaches and phishing at 16% of breaches.” On average, the costliest initial attack vector was phishing at USD 4.91 million, followed by business email compromise at USD 4.89 million.
With that in mind, this article contains important tips and tools to help both cybersecurity analysts and general users on how to detect possible threats associated with phishing e-mails.
Spoofing & how to detect a Suspicious E-mail
Attackers can send emails on behalf of someone else, as the e-mail messages do not necessarily have an authentication mechanism. This kind of technique is called spoofing, and is used to make the user believe that the incoming email is reliable.
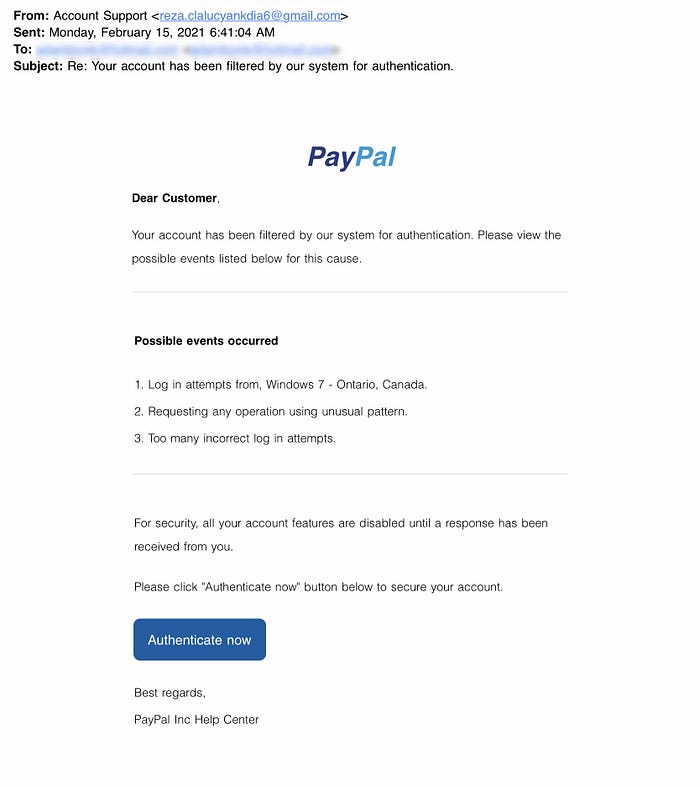
An example of suspicious e-mail can be seen as below, where the sender domain belongs to a public address anyone can have (‘@gmail.com’), and not a corporative e-mail (‘@paypal.com’).
A common technique threat actors have is to perform phishing attacks using mostly free, and legal platforms. Such as:
- Services that offer Cloud Storage such as Google and Microsoft: Attackers try to use Google / Microsoft drive addresses that seem harmless to the user by uploading harmful files onto the drive.
- Free subdomains services such as Google, Wordpress, Blogspot, Wix, GoDaddy: Threat actors try to deceive security products and analysts by creating a free subdomain from these services. Since whois information cannot be searched as a subdomain, it can be seen that these addresses were taken in the past and belongs to the actual institutions.
- Form applications: Services are available that allow free form creation. Since the domain is harmless under normal conditions, it can pass on to the user without getting stuck on antivirus software. Google Forms is an example of these services. When looking at whois information, the domain can be seen to be Google, so the attacker can mislead further analysts.
Structure of an Email Header
Before learning how to conduct an email analysis, it is important that we know how the structure of an e-mail header works.
- From - The sender’s address;
- To - The receiver’s address, including CC and BCC;
- Date - Timestamp, when the email was sent;
- Subject - The subject of the email;
- Return Path - The return address of the reply, a.k.a. “Reply-To”. If you reply to an email, the reply will go to the address mentioned in this field;
- Domain Key and DKIM Signatures - Email signatures are provided by email services to identify and authenticate emails;
- SPF - Shows the server that was used to send the email. It will help to understand if the actual server is used to send the email from a specific domain;
- Message-ID - Unique ID of the email;
- MIME-Version - Used MIME version. It will help to understand the delivered “non-text” contents and attachments;
- X-Headers - The receiver mail providers usually add these fields. Provided info is usually experimental and can be different according to the mail provider;
- X-Received - Mail servers that the email went through;
- X-Spam Status - Spam score of the email;
- X-Mailer - Email client name.
Important Email Header Fields for Quick Analysis
Questions to Ask / Required Checks and Evaluations:
- Do the “From”, “To”, and “CC” fields contain valid addresses? Having invalid addresses is a red flag.
- Are the “From” and “To” fields the same? Having the same sender and recipient is a red flag.
- Are the “From” and “Return-Path” fields the same? Having different values in these sections is a red flag.
- Was the email sent from the correct server? Email should have come from the official mail servers of the sender.
- Does the “Message-ID” field exist, and is it valid? Empty and malformed values are red flags.
- Do the hyperlinks redirect to suspicious/abnormal sites? Suspicious links and redirections are red flags.
- Do the attachments consist of or contain malware? Suspicious attachments are a red flag. File hashes marked as suspicious/malicious by sandboxes are also a red flag.
Tools to use During an Analysis
Email Client Apps
One of the fastest ways to see the visual contents of an “.eml” file is by opening it directly on an e-mail client like Thunderbird or Outlook.
Althought it’s a good way to get the visuals for your report, it’s not reccomended to open such files in your desktop machine. You can always download an e-mail client on a virtual machine instead or use text editors to see its content.

Text Editors
You can use a text editor of your own choice (Vim, Nano, Sublime, Visual Studio, EmEditor..) to view email files without opening and executing any of the linked attachments/commands.
emlAnalyzer
Text editors are helpful in analysis, but there are some tools that can help you to view the email details in a clearer format.
We can use the “emlAnalyzer” tool to view the body of the email and analyze the attachments. The emlAnalyzer is a tool designed to parse email headers for a better view and analysis process.
It can be used to show the headers, body, embedded URLs, plaintext, HTML data, and attachments. The sample usage query is explained below.
Query Details Explanation
- emlAnalyzer: Main command
- -i: File to analyse
-i /path-to-file/filename
Note: Remember, you can either give a full file path or navigate to the required folder using the “cd” command. - -header: Show header
- -u: Show URLs
- -text: Show cleartext data
- -extract-all: Extract all attachments
An example of usage of the tool can be seen as below.

PhishTool
PhishTool is another useful tool for the automation of the analysis process, as it collects the necessary information — headers, body, embedded URLs, plaintext, HTML attachments… of selected .eml files in a way that’s easier for the comprehension.

An example of usage of the tool can be seen as below, after registering on the platform from PhishTool.

Open Source Intelligence (OSINT)
Additionally, you can use some Open Source Intelligence (OSINT) tools to check email reputation and enrich the findings. You can visit the given sites below and do a reputation check on the sender address and the address found in the return path.
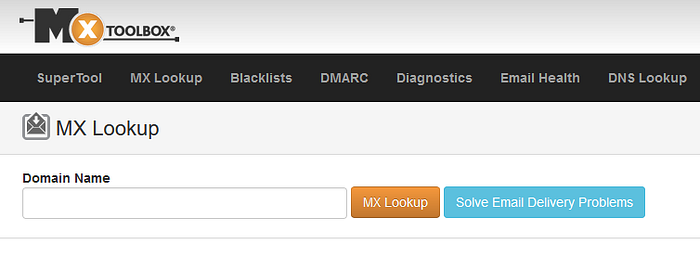
MxToolbox
The MX Record Lookup tool is an online tool that lets you query DNS servers and get instant results. Mail Exchanger or MX lookups are used to determine the MX records associated with a domain, it can also be used to check out whether a domain is blacklisted or not.
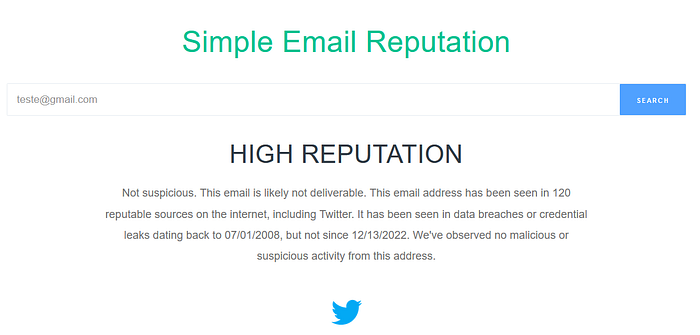
emailrep.io
Tool used to detect targeted phishing attacks and e-mail reputation.
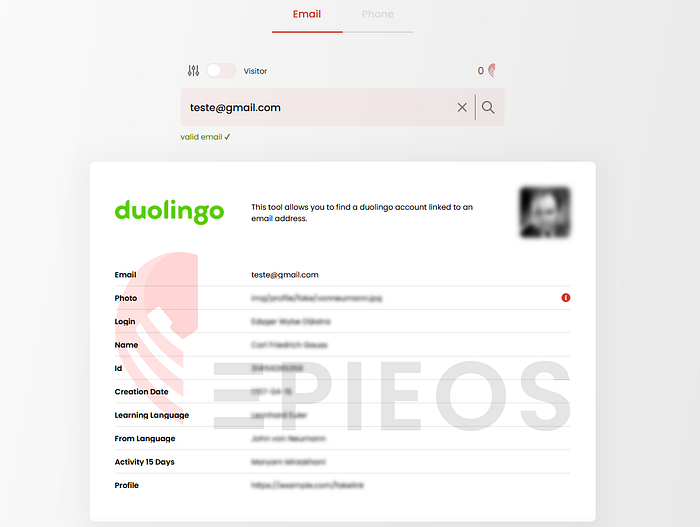
Epieos
Tool for the gathering of information of accounts linked to an e-mail address (can be efficient with ‘@gmail.com’ addresses).
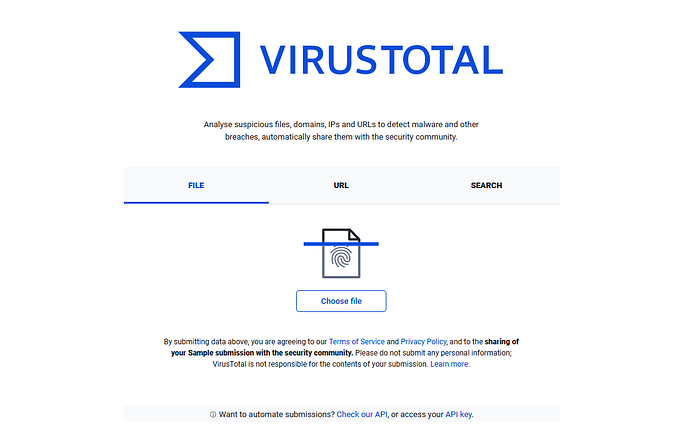
VirusTotal
A service that provides a cloud-based detection toolset and sandbox environment. It can be used to collect indicators of compromise, and static analysis of suspicious files.
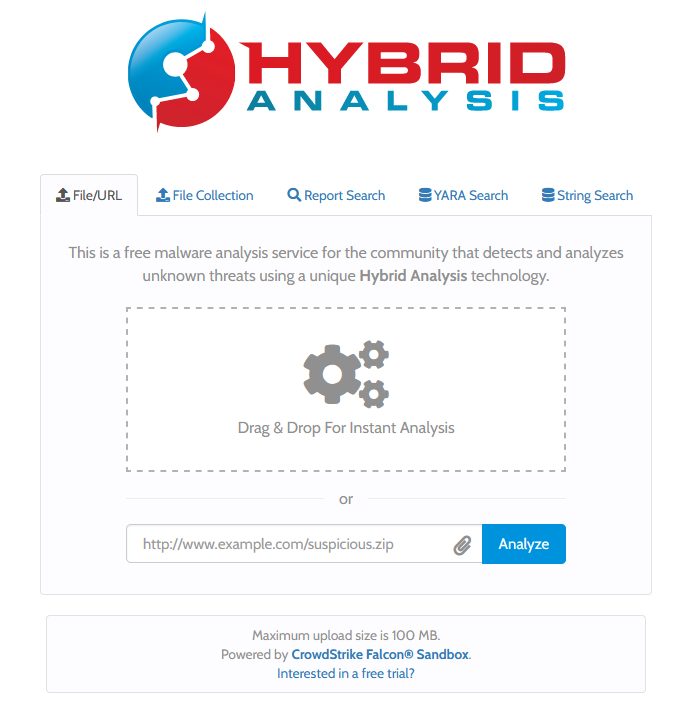
Hybrid Analysis
An alternative sandbox environment for VirusTotal, it detects possible IOCs, TTPs and gives a static analysis of malicious files.
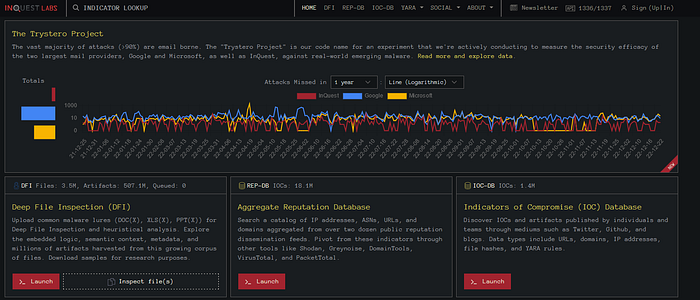
InQuest Labs
A service that provides network and file analysis by using threat analytics.
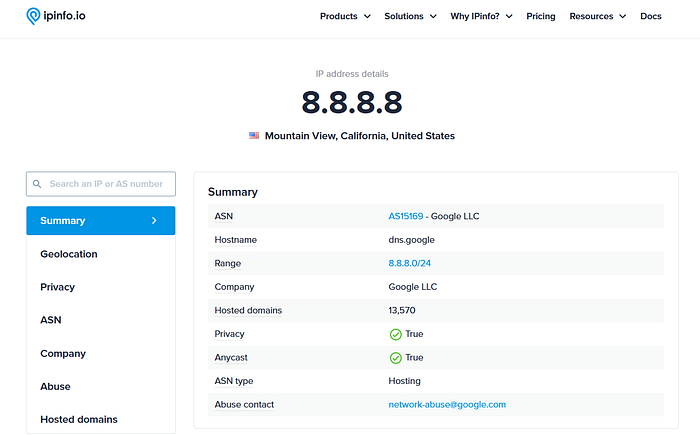
IPinfo.io
A service that provides detailed information about an IP address by focusing on geolocation data and service provider.
Talos Reputation
An IP reputation check service provided by Cisco Talos.
Urlscan.io
A service that analyses websites by simulating regular user behaviour.

Browserling
A browser sandbox used to test suspicious/malicious links.
Wannabrowser
Another browser sandbox used for the testing of suspicious/malicious links.
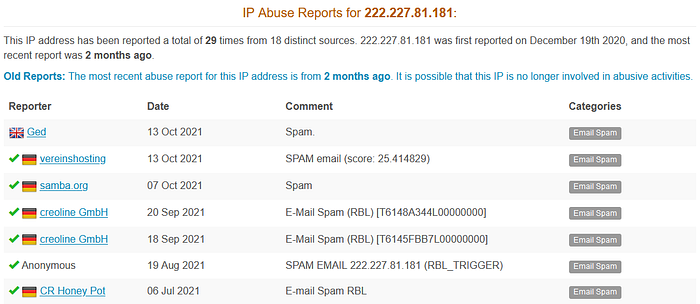
AbuseIPDB
AbuseIPDB is a project dedicated to helping combat the spread of hackers, spammers, and abusive activity on the internet. It can be useful to see and send abuse reports related to certain IP or Domain Addresses.
Example of Analysis
After getting to know most used concepts and tools, we can finally analyze the contents of an e-mail header.
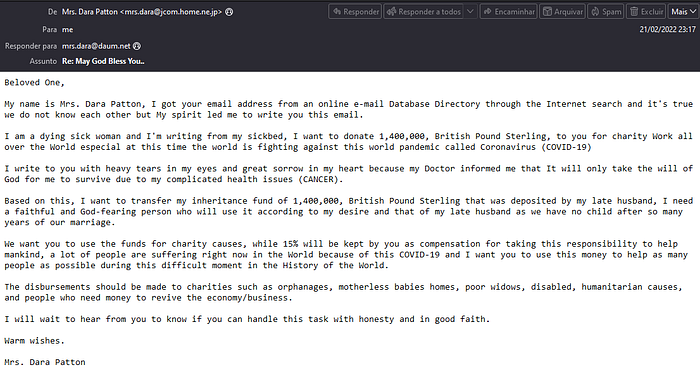
Points of Attention
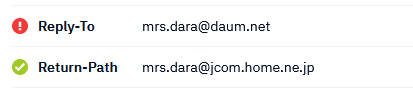
- Both the Reply-to and Return-Path of the sender adress contains different e-mail addresses;

- The IP Address of the sender is 222.227.81.181, and the message date (when it was sent) is Monday - 21 of February, 2022;
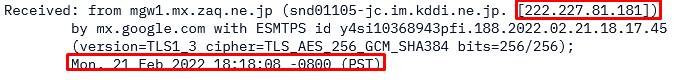
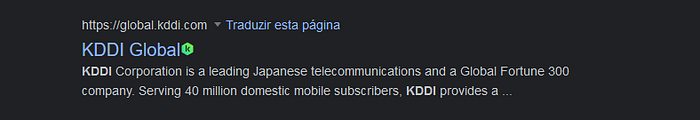
- The IP address ‘222.227.81.181’ is from Japan, under the domain “kddi.ne.jp”;
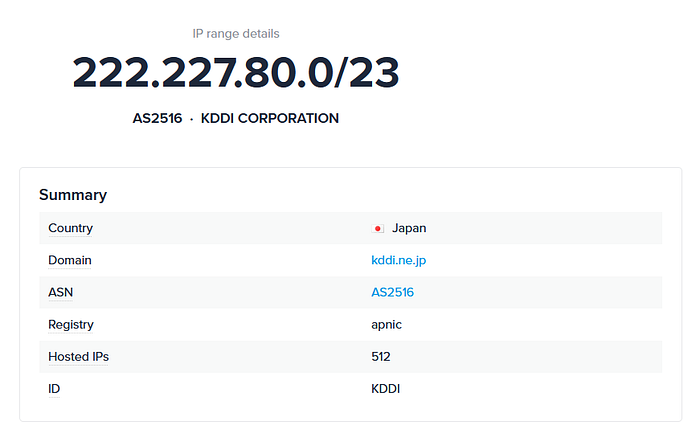
Looking up “KDDI Corporation”, we can tell it is a possible legitimate service being useed by third parties.
- We can also search for information about the DNS address of the sender: “snd01105-jc.im.kddi.ne.jp”;

It’s possible to find publications on the forums “romancescam” and “scamsurvivors” relating spam mails from that same DNS address.
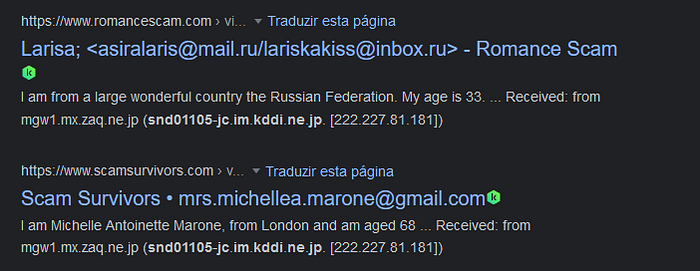
With that we can confirm more suspicious messages were sent from the DNS Address “snd01105-jc.im.kddi.ne.jp” also using the following tactics:
- Reply-to is different from the Return-Path listed;
- “KDDI Corporation” is also the provider of the Return-path;
- Message is also under the pretext of a person who is sick, dying, and needs someone else to do “good deeds” with their money.
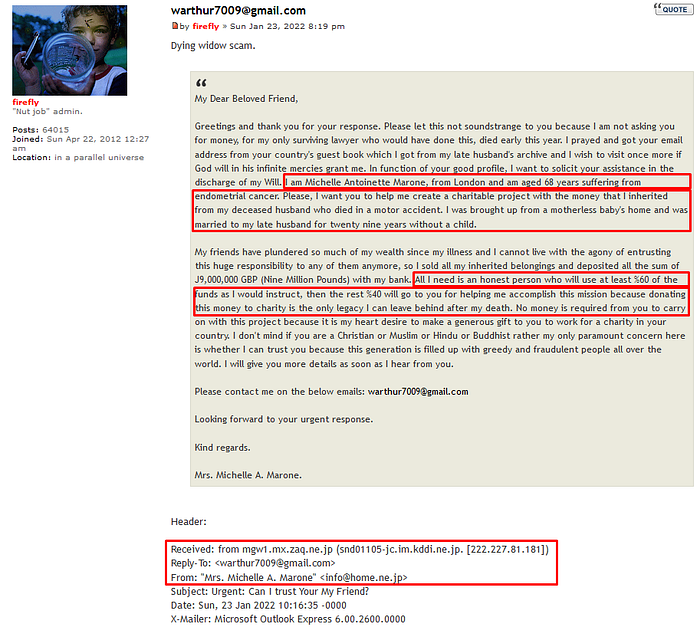
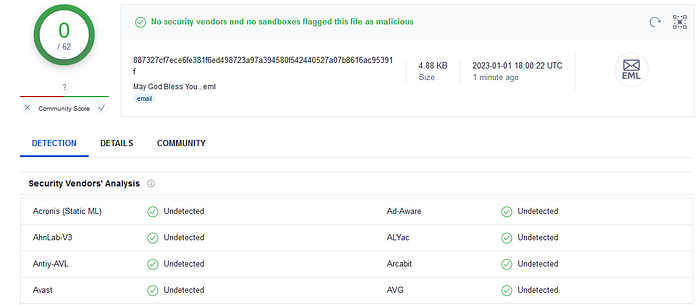
- There‘s no malicious attachments related to that e-mail and static analysis tools couldn’t really detect any possible threat;

- The suspicious IP Address ‘222.227.81.181’ has also been reported a total of 29 times from 18 distinct sources on AbuseIPDB, mostly as a detected spam.
Conclusion of Analysis
Although no malicious attachments or links were found, the information that the ‘Reply-To’ email address ‘mrs.dara@daum.net’ is inconsistent with the ‘From’ e-mail ‘mrs.dara@jcom.home.ne.jp’ is suspicious.
When attempting to persuade a phishing target to respond, attackers often provide a different ‘Reply-To’ email address whilst spoofing a legitimate ‘From’ email address.
An unsuspecting target might reply to the phishing email believing they are replying to the email address shown prominently in their email client, when the response is actually being sent to the ‘Reply-To’ email address.
This could be a social engineering tactic to get financial information from the victim under the assumption they would actually receive the money. With a quickly research, it was also possible to find scam reports associated with the same DNS address, which concludes the sender of the message should not be trusted.
References:
- TryHackMe: Advent of Cyber 2022 - Day 6: E-mail Analysis: https://tryhackme.com/room/adventofcyber4
- LetsDefend - Phishing Email Analysis: https://app.letsdefend.io/training/lessons/phishing-email-analysis
- Phishing Attacks: A Recent Comprehensive Study and a New Anatomy: https://www.frontiersin.org/articles/10.3389/fcomp.2021.563060/full
- Examples of Phishing Email: 20 Emails That Don’t Look Like It: https://www.aura.com/learn/phishing-email-examples#3.-Suspicious-activity-notice
